About the CoMSES Model Library more info
Our mission is to help computational modelers develop, document, and share their computational models in accordance with community standards and good open science and software engineering practices. Model authors can publish their model source code in the Computational Model Library with narrative documentation as well as metadata that supports open science and emerging norms that facilitate software citation, computational reproducibility / frictionless reuse, and interoperability. Model authors can also request private peer review of their computational models. Models that pass peer review receive a DOI once published.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and feel free to contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 1127 results for "Oto Hudec" clear search
BN intervention model
Di Wang | Published Wednesday, July 13, 2011 | Last modified Saturday, April 27, 2013Bayesian network is used to modelling the behavior of an individual level and multi-agent system is used to simulate the meme diffusion through the whole network.
A-KinGDom: A Kinship, Grooming and Dominance Model for Primate Societies
Ruth Dolado Francesc S Beltran Vicenc Quera | Published Thursday, July 11, 2013 | Last modified Wednesday, July 17, 2013A-KinGDom simulates the emergence of the social structure in a group of non-human primates. The model includes dominance and affiliative interactions which allow us to define four different attack and affiliative strategies.
Investor-based electricity market model
Oscar Kraan | Published Monday, January 02, 2017 | Last modified Friday, October 12, 2018The model is a representation of a liberalised electricity market designed as an energy-only market and consists of large scale investors and their power generation assets in the electricity market.
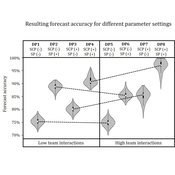
Demand Planning Model
Iris Lorscheid Jonas Hauke Matthias Meyer | Published Wednesday, October 04, 2017Demand planning requires processing of distributed information. In this process, individuals, their properties and interactions play a crucial role. This model is a computational testbed to investigate these aspects with respect to forecast accuracy.
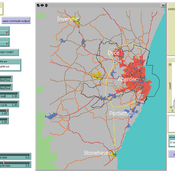
Transport simulation in a real road network
Gary Polhill Jiaqi Ge | Published Tuesday, April 17, 2018 | Last modified Tuesday, April 17, 2018Ge, J., & Polhill, G. (2016). Exploring the Combined Impact of Factors Influencing Commuting Patterns and CO2 Emission in Aberdeen Using an Agent-Based Model. Journal of Artificial Societies and Social Simulation, 19(3). http://jasss.soc.surrey.ac.uk/19/3/11.html
We develop an agent-based transport model using a realistic GIS-enabled road network and the car following method. The model can be used to study the impact of social interventions such as flexi-time and workplace sharing, as well as large infrastructure such as the construction of a bypass or highway. The model is developed in Netlogo version 5 and requires road network data in GIS format to run.
The Regional Security Game: An Agent-based, Evolutionary Model of Strategic Evolution and Stability
Anthony Skews | Published Saturday, June 09, 2018The Regional Security Game is a iterated public goods game with punishement based on based on life sciences work by Boyd et al. (2003 ) and Hintze & Adami (2015 ), with modifications appropriate for an international relations setting. The game models a closed regional system in which states compete over the distribution of common security benefits. Drawing on recent work applying cultural evolutionary paradigms in the social sciences, states learn through imitation of successful strategies rather than making instrumentally rational choices. The model includes the option to fit empirical data to the model, with two case studies included: Europe in 1933 on the verge of war and south-east Asia in 2013.
Roman Amphora reuse
Tom Brughmans | Published Wednesday, August 07, 2019 | Last modified Wednesday, March 15, 2023UPDATE in V1.1.0: missing input data files added; relative paths to input data files changed to “../data/FILENAME”
A model that allows for representing key theories of Roman amphora reuse, to explore the differences in the distribution of amphorae, re-used amphorae and their contents.
This model generates simulated distributions of prime-use amphorae, primeuse contents (e.g. olive oil) and reused amphorae. These simulated distributions will differ between experiments depending on the experiment’s variable settings representing the tested theory: variations in the probability of reuse, the supply volume, the probability of reuse at ports. What we are interested in teasing out is what the effect is of each theory on the simulated amphora distributions.
…
Peer reviewed SWIRS Spread of a woody invader in riparian systems
Moira Zellner Beatriz Sosa Carlos Andrés Chiale | Published Tuesday, May 09, 2023Riparian forests are one of the most vulnerable ecosystems to the development of biological invasions, therefore limiting their spread is one of the main challenges for conservation. The main factors that explain plant invasions in these ecosystems are the capacity for both short- and long-distance seed dispersion, and the occurrence of suitable habitats that facilitate the establishment of the invasive species. Large floods constitute an abiotic filter for invasion.
This model simulates the spatio-temporal spread of the woody invader Gleditsia. triacanthos in the riparian forest of the National Park Esteros de Farrapos e Islas del Río Uruguay, a riparian system in the coast of the Uruguay river (South America). In this model, we represent different environmental conditions for the development of G. triacanthos, long- and short-distance spread of its fruits, and large floods as the main factor of mortality for fruit and early stages.
Field results show that the distribution pattern of this invasive species is limited by establishment, i.e. it spreads locally through the expansion of small areas, and remotely through new invasion foci. This model recreates this dispersion pattern. We use this model to derive management implications to control the spread of G. triacanthos
SBH trust model
Di Wang | Published Tuesday, December 14, 2010 | Last modified Saturday, April 27, 2013This is a computational model to articulate the theory and test some assumption and axioms for the trust model and its relationship to SBH.
An empirical ABM for regional land use/cover change: a Dutch case study
Diego Valbuena | Published Saturday, March 12, 2011 | Last modified Thursday, November 11, 2021This is an empirical model described in http://dx.doi.org/10.1016/j.landurbplan.2010.05.001. The objective of the model is to simulate how the decision-making of farmers/agents with different strategies can affect the landscape structure in a region in the Netherlands.
Displaying 10 of 1127 results for "Oto Hudec" clear search